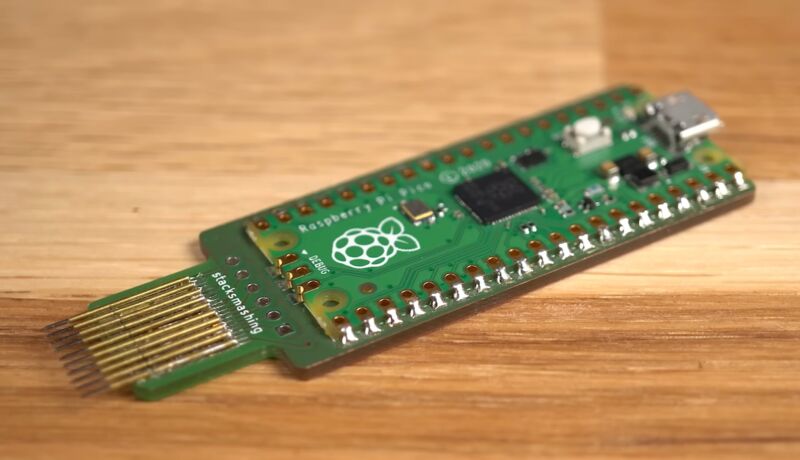
Last week, a video by security researcher StackSmashing demonstrated an exploit that could break Microsoft’s BitLocker drive encryption in “less than 50 seconds” using a custom PCB and a Raspberry Pi Pico.
The exploit works by using the Pi to monitor communication between an external TPM chip and the rest of the laptop, a second-generation ThinkPad X1 Carbon from roughly 2014. The TPM stores the encryption key that unlocks your encrypted disk and makes it readable, and the TPM sends that key to unlock the disk once it has verified that the rest of the PC’s hardware hasn’t changed since the drive was encrypted. The issue is that the encryption key is sent in plaintext, allowing a sniffer like the one that StackSmashing developed to read the key and then use it to unlock the drive in another system, gaining access to all the data on it.
This is not a new exploit, and StackSmashing has repeatedly said as much. We reported on a similar TPM sniffing exploit in 2021, and there’s another from 2019 that similarly used low-cost commodity hardware to pick up a plaintext encryption key over the same low-pin count (LPC) communication bus StackSmashing used. This type of exploit is well-known enough that Microsoft even includes some extra mitigation steps in its own BitLocker documentation; the main new innovation in StackSmashing’s demo is the Raspberry Pi component, which is likely part of the reason why outlets like Hackaday and Tom’s Hardware picked it up in the first place.
The original video is pretty responsible about how it explains the exploit, and that first wave of re-reporting at least mentioned important details, like the fact that the exploit only works on systems with discrete, standalone TPM chips or that it’s broadly similar to other well-documented, years-old attacks. But as the story has circulated and re-circulated, some reporting has excluded that kind of nuance, essentially concluding that the drive encryption in all Windows PCs can be broken trivially with $10 of hardware and a couple minutes of time. It’s worth clarifying what this exploit is and isn’t.
What PCs are affected?
BitLocker is a form of full-disk encryption that exists mostly to prevent someone who steals your laptop from taking the drive out, sticking it into another system, and accessing your data without requiring your account password. Many modern Windows 10 and 11 systems use BitLocker by default. When you sign into a Microsoft account in Windows 11 Home or Pro on a system with a TPM, your drive is typically encrypted automatically, and a recovery key is uploaded to your Microsoft account. In a Windows 11 Pro system, you can turn on BitLocker manually whether you use a Microsoft account or not, backing up the recovery key any way you see fit.
Regardless, a potential BitLocker exploit could affect the personal data on millions of machines. So how big of a deal is this new example of an old attack? For most individuals, the answer is probably “not very.”
One barrier to entry for attackers is technical: Many modern systems use firmware TPM modules, or fTPMs, that are built directly into most processors. In cheaper machines, this can be a way to save on manufacturing—why buy a separate chip if you can just use a feature of the CPU you’re already paying for? In other systems, including those that advertise compatibility with Microsoft’s Pluton security processors, it’s marketed as a security feature that specifically mitigates these kinds of so-called “sniffing” attacks.
That’s because there is no external communication bus to sniff for an fTPM; it’s integrated into the processor, so any communication between the TPM and the rest of the system also happens inside the processor. Virtually all self-built Windows 11-compatible desktops will use fTPMs, as will modern budget desktops and laptops. We checked four recent sub-$500 Intel and AMD laptops from Acer and Lenovo, and all used firmware TPMs; ditto for four self-built desktops with motherboards from Asus, Gigabyte, and ASRock.
Ironically, if you’re using a high-end Windows laptop, your laptop is slightly more likely to be using a dedicated external TPM chip, which means you might be vulnerable.
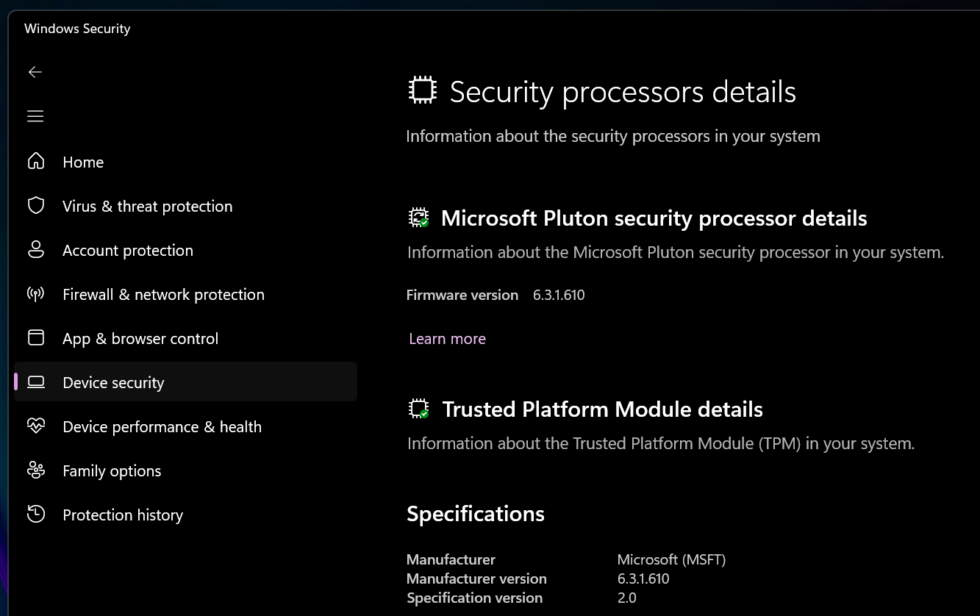
The easiest way to tell what type of TPM you have is to go into the Windows Security center, go to the Device Security screen, and click Security Processor Details. If your TPM’s manufacturer is listed as Intel (for Intel systems) or AMD (for AMD systems), you’re most likely using your system’s fTPM, and this exploit won’t work on your system. The same goes for anything with Microsoft listed as the TPM manufacturer, which generally means the computer uses Pluton.
But if you see another manufacturer listed, you’re probably using a dedicated TPM. I saw STMicroelectronics TPMs in a recent high-end Asus Zenbook, Dell XPS 13, and midrange Lenovo ThinkPad. StackSmashing also posted photos of a ThinkPad X1 Carbon Gen 11 with a hardware TPM and all the pins someone would need to try to nab the encryption key, as evidence that not all modern systems have switched over to fTPMs—admittedly something I had initially assumed, too. Laptops made before 2015 or 2016 are all virtually guaranteed to be using hardware TPMs when they have them.
That’s not to say fTPMs are completely infallible. Some security researchers have been able to defeat the fTPMs in some of AMD’s processors with “2–3 hours of physical access to the target device.” Firmware TPMs just aren’t susceptible to the kind of physical, Raspberry Pi-based attack that StackSmashing demonstrated.
It will usually take more than one minute
The other barriers to entry are equipment, time, and expertise. The Raspberry Pi-based version of this attack lowers all three of these barriers a bit, in that the equipment is cheap and easy to find and the software has already been written for you. But other TPM-sniffing attacks also used relatively cheap hardware and came with extensive documentation.
The thing preventing a lot of casual hackers from doing this to some random person’s laptop is the fragmentation of the PC ecosystem—the specific PCB built by StackSmashing works in a second-generation X1 Carbon and may also work well in other Lenovo laptops of a similar vintage. But a newer ThinkPad, or another computer from Dell, HP, Microsoft, Asus, Acer, or any other manufacturer, will keep its discrete TPM chip (if it has one) in a different place. And you’d need to figure out what pins or pads to use to access the communication bus on a laptop-to-laptop basis.
If there’s one slightly sensationalist bit to the StackSmashing video, it’s the claim that this exploit takes less than 50 seconds. It’s true that that’s as long as it takes the tool to collect the encryption key for this laptop, but it downplays the fact that this was done using a laptop he had already torn apart, using a tool on a custom PCB that he had built specifically to interface with easily accessible contact pads.
So it’s quick and easy to break the encryption on other laptops with identical setups but less so if you’re working with hardware you’ve never seen before. Microsoft’s description of someone who can do this—an “attacker with skill and lengthy physical access”—seems accurate to me.
So what can you do about it?
Most individual users don’t need to worry about this kind of attack; many consumer systems don’t use dedicated TPM chips at all, and accessing your data requires a fairly skilled attacker who is very interested in pulling the data off of your specific PC rather than wiping it and reselling it or stripping it for parts. (This is not true of business users who deal with confidential information on their work laptops, but their IT departments hopefully do not need me to tell them that.)
If you do want to give yourself an extra layer of protection, Microsoft recommends setting up an enhanced PIN that is required at startup, in addition to the theoretically sniffable key that the TPM provides. IT admins can enable this remotely via Group Policy; to enable it on your own system, open the Local Group Policy Editor (Windows + R, type gpedit.msc, hit Enter). Then navigate to Computer Configuration > Administrative Templates > Windows Components > Bitlocker Driver Encryption > Operating System Drives, and enable both the “require additional authentication at startup” and “allow enhanced PINs for startup” settings.
Then run a Command Prompt window as an administrator and type manage-bde -protectors -add c: -TPMAndPIN; you’ll be prompted to set a PIN for the drive. Once you’ve done this, the next time you boot, the system will ask for a PIN before it boots into Windows.
In some cases, an attacker with physical access to your system and a sufficient amount of time may be able to gain access by brute-forcing this PIN, which is why it’s important to make it complex, like any good password.
A highly motivated, technically skilled attacker with extended physical access to your device may still be able to find a way around these safeguards. Regardless, having disk encryption enabled keeps your data safer than it would be with no encryption at all, and that will be enough to deter a lot of less-skilled, casual attackers from being able to get at your stuff.